On the other hand, it’s crucial to look at stability measures when making these addresses to guard your money and forestall unauthorized obtain.
Hardware wallets are deemed probably the most safe variety of Ethereum wallet. They're Bodily products that store your private keys offline. At the start, these wallets are non-custodial, which means you've got correct possession in excess of your funds.
Both contract addresses and multi-signature addresses are crucial components with the Ethereum ecosystem, enabling the execution of clever contracts and improving the safety of transactions within the Ethereum blockchain.
Private Crucial Place: Here are some code examples, determined by the elliptic curve secp256k1 employed by ethereum, as Other people have observed to ensure that the 256-bit crucial being legitimate, it need to be smaller in comparison to the curve's parameter n that is also a 256-bit price that may be prepared in hexadecimal structure as: 0xfffffffffffffffffffffffffffffffebaaedce6af48a03bbfd25e8cd0364141
SecurityException - if a stability manager exists and its checkConnect process isn't going to enable the Procedure
Components Wallets: Components wallets like Ledger and Trezor give a safe strategy to generate and keep your Ethereum addresses. These Bodily gadgets keep your private keys offline, protecting them from potential online threats. They offer a better level of safety compared to on the internet wallets.
The information on this Web site is standard in mother nature. You should take into consideration the data in light-weight of your targets, economical situation and needs.
The deploying account’s address and also the nonce worth are concatenated. We concatenate the deploying account’s address plus the nonce benefit: 0x0123456789abcdef0123456789abcdef01234565
Implies the caching coverage for prosperous identify lookups in the title assistance. The value is specified as as integer to indicate the number of seconds to cache the prosperous lookup.
Given the title of a bunch, returns an variety of its IP addresses, based upon the configured name provider over the method. The host title can possibly be considered a device identify, like "java.Sunshine.com", or a textual representation of its IP address. If a literal IP address is provided, just the validity of the address format is checked. For host laid out in literal IPv6 address, possibly the shape defined in RFC 2732 or even the literal IPv6 address structure defined in RFC 2373 is accepted.
Usually, you cannot initialize a hardware wallet using this method as the 24 term recovery phrase they use is not the same detail for a private essential accustomed to signal transactions. The 24 word Restoration phrase is accustomed to derive numerous private keys for different types of copyright the wallet retains.
To develop new contracts: Each time a new contract is established, it truly is assigned the zero address. The contract’s address is then current after the transaction is mined.
The unspecified address must not be employed since the place address of an IP packet. The Loopback Addresses -- This can be the address assigned into the loopback interface. Everything despatched to this IP address loops close to and will become IP enter within the regional host. This address is often employed Click for More Info when testing a customer.
If shadow fork from file is the preferred solution, then please ensure the most current block json reaction is gathered together with
 Mason Gamble Then & Now!
Mason Gamble Then & Now! Ross Bagley Then & Now!
Ross Bagley Then & Now! Anthony Michael Hall Then & Now!
Anthony Michael Hall Then & Now!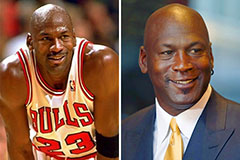 Michael Jordan Then & Now!
Michael Jordan Then & Now! Bernadette Peters Then & Now!
Bernadette Peters Then & Now!